from Lemmchen@feddit.org to selfhosted@lemmy.world on 15 May 20:14
https://feddit.org/post/29898434
Recently I’ve installed luci-app-banip on my OpenWrt router and blocked most countries from accessing my services on my network. Not seeing why I would want any of that traffic I also blocked the whole of the ARIN registry, responsible for IP addresses from Canada and the United States.
Edit: Note this is only for inbound traffic. Outbound traffic is allowed no matter the target country.
Fast forward a few weeks and my certbot renewals fail with the following error: Failed to renew certificate enter.domain.here with error: HTTPSConnectionPool(host=‘acme-v02.api.letsencrypt.org’, port=443): Read timed out. (read timeout=45)
Confused af I start looking for solutions and as so often only find useless or completely ridiulous solutions (lowering my MTU to 1300, what? WHY?). Finally I find some enlighted figure that says they recently enabled a blocklist for certain countries and that was the issue for them.
Now I make the connection to my use of banIP, re-allow the USA and my cert renewals start working again. Hooray!
However, there are two things bothering me:
- Why would such a block even interrupt my renewals? I’m using DNS challenges and the ACME servers should only check the DNS entries, not where those entries actually redirect to. The DNS server/root isn’t in my home network, so isn’t affected by any firewall shenanigans I do here.
- How can I make an exception for the Let’s Encrypt ACME servers while blocking the rest of the ARIN IP space?
I see there’s the option for ASN selection and external allowlists:
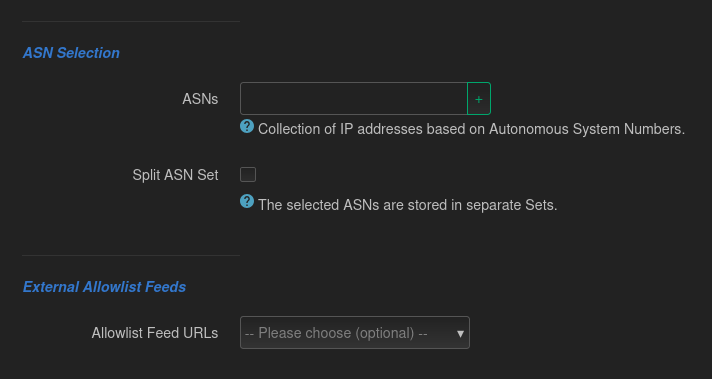
Does anybody have an idea on how to configure this so that Let’s Encrypt continues to work without compromising on my network security?
(Edit: And just for clarity, I do not live in the US or anywhere on the American continent.)
threaded - newest
Forgive my ignorance as I am very new to networking. Does it not look like it is the other way around? Your certificate manager tries to connect to Let’s Encrypt and fails? Even with DNS challenges, your certificate manager has to tell Let’s Encrypt to check your DNS records somehow.
Outbound traffic has never been blocked, so it’s not a matter of me or my “certificate manager” being able to reach Let’s Encrypt.
are you using external DNS hosting? is it in a (now) blocked country? if so, then your local certbot is unable to update the DNS server records (return traffic from your DNS host is being blocked by your iptables/nftables config).
yeah, that would suggest an https renewal method. had you previously configured web server renewal at all before switching over to DNS? any other suspicious notifications in the logs?
edit: in thinking about this a little more… the renewal has to be initiated by your host, and that is likely done via https (you talk https to the acme server and tell it you want a renewal by DNS). so, if you are blocking the acme servers then the same issue applies - no return traffic.
I’ve been using DNS challenge for this domain from the start. I’m not sure what you mean by external DNS hosting. The domain is from netcup, the certbot host runs in my local network (as does the HTTP server that the domain points to).
Netcup is a German hosting company, I live in Germany, inbound traffic from Germany is NOT blocked on my router, outbound traffic isn’t blocked at all.
not hosting your own DNS server. specifically it sounds like your DNS server is hosted on your domain provider, not your own local network. you have set up certbot to automatically configure your remotely hosted DNS server for the DNS based renewal.
if DNS based recert was working before then it should be working now.
as I said in my edit, you are likely blocking the return https traffic from the US based let’s encrypt acme servers - so your initial diagnostic is correct. your local firewall is likely stopping the acme servers from talking back to your local host.
you are right back where you started, asking for info in how to allow-list the acme IP ranges. but at least we may now know why it is not working and you are seeing an https timeout even though you are using DNS based certificate renewals.
edit: typos
AFAICT it is using DNS challenges, unless the cerbot netcup plugin somehow does stuff it shouln’t need to do.
agreed. you are using DNS-01 challenges. so the workflow is…
your local certbot machine initiates an https connection to the letsencrypt servers to start the DNS-01 challenge. during this HTTPS dialog, your local certbot is informed of the key material to insert into your DNS records. your local certbot then modifies your netcup DNS server (hosted remotely, not on your local network) with the keying material and the letsencrypt servers verify that the keys are actually there, proving that you control the domain. the letsencrypt serves then issue you the certificate (again, via HTTPS) and your local certbot stores it in your local host.
the issue is most likely stems from the initial HTTPS connection that certbot tries to make to the let’s encrypt servers. while your firewall allows this traffic out, it does not allow return traffic back in because of your explicit blocking of US (and perhaps other) based addresses.
even through your are using DNS for your domain autentocation, your local host - the machine running certbot - is unable to initiate the certificate transfer because of the firewall blocking return traffic.
the two external networks (and, therefore IP ranges/subnets/etc) that are important here are the let’s encrypt servers and the netcup DNS servers. certbot will have to talk to both of these in order to function.
@Lemmchen The letsencrypt acme server IP addresses aren't published and rotate frequently to prevent mitm attacks near the source. Placing them on an allowlist is not the solution you're looking for.
What is, then? Do they provide European ACME servers I could use instead?
@Lemmchen Only open the port when you're expecting an acme verification. Or do DNS-based verification.
That’s the thing. I am doing DNS challenges. I’m using a certbot plugin for my DNS provider (github.com/coldfix/certbot-dns-netcup) to automatically have my DNS entries set up for it.
@Lemmchen Then the acme verification is hitting your provider's DNS servers (or rather, one of the DNS servers listed as authoritative with your registrar) and the verifier never needs to hit your infrastructure directly.
Unless you're hosting your own DNS and for some reason want to apply a blocklist to that.
That’s what I don’t get. Firewall up, renewal timeout. Firewall down, renewals work just fine. This shouldn’t happen for DNS challenges, but for some reason it apparently does.
Check your firewall’s block log, because what you describe should not be happening.
Assuming that the ‘enter.domain.here’ is a masking of the real domain, I would have to wonder if the acme client is actually trying to use the http validation rather than DNS. You could pcap on the outside to look for it coming in to confir.
As for filtering to specifically allow their addresses, I think their system has a unique user agent that you could filter against, or use an inbound proxy to allow global access to the ‘/.well-known/acme-challenge/’ path while keeping the rest of the site blocked.
enter.domain.hereis simply a redaction of my real domain as I did not want to doxx myself.Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
5 acronyms in this thread; the most compressed thread commented on today has 21 acronyms.
[Thread #293 for this comm, first seen 15th May 2026, 21:40] [FAQ] [Full list] [Contact] [Source code]
Ok, bare with me, I’ve had roo muxh to drink, but, don’t ban the world, only allow countries you want.
Now, Let’s Encrypt is a US entity, so whilst you might not want to allow the US in, perhaps allow <whatever> countries + Let’s Encrypt subnet
Also… still block some countries for outbound too… like blocking any C&C destinations.
If I’m waay off, sorry, I’ll try to respond in the morning when I’m not drunk.
So I am pretty sure that error is happening because certbot can’t retrieve the certificate which is coming from that API no matter what type of challenge you are using (this is what ACME is).
Now when you say you are blocking inbound traffic, have you made an exception for established outbound session return traffic? If not then you your inbound rule will block all traffic because without that exception the explicit deny will typically override any session/stateful based rules your firewall might have by default (this applies to most firewall vendors I have run into).
That said, I’m not sure what your goal is but blocking outbound traffic to those ASN might be more effective for you anyway because your firewall should already be dropping any inbound traffic that isn’t otherwise allowed so I’m not sure blocking inbound traffic really gains you anything but I’m just guessing. Hope that all makes sense!
Firewalls are typically built using ‘in’ rules, but it’s not referring to ‘wan > lan’ but rather if the rule is processed on the ingress of the firewall or the egress.
Stateful firewalls sessions are always going to allow responses, the old request that someone needs a rule ‘both directions’ is something of a running joke at this point honestly.
A pcap would explain a lot, the fact that the error cites a specific domain does sound like an outbound attempt, but if it was a specifically inbound region block that wouldn’t add up.
Well, blocking inbound traffic from these countires is part of my firewall. I have some services that are exposed on the internet, but I don’t want the whole world to hammer these services, scrape them and potentially exploit vulnerabilities on them. I know a VPN would be more effective here, but that’s not an option for every service.